- Home
- /
- Offensive Security
Offensive Security
- Security Engineering & Implementation
Build. Configure. Secure Real Infrastructure.
RootSecured’s Security Engineering & Implementation module provides hands-on training in deploying and securing enterprise-grade security solutions across networks, systems, and user environments.

Overview
Security is not only about identifying threats — it is about implementing the right controls to prevent them. Security Engineering focuses on designing, configuring, and managing security solutions used in real-world environments.
This module trains students to work on actual security tools and technologies, enabling them to implement and manage enterprise security infrastructure.
- What You Will Learn
Learn to Build and Secure Enterprise-Grade Security Systems
Gain hands-on experience in configuring firewalls, deploying SIEM solutions, managing identity access, and implementing data protection controls. This module focuses on real-world security engineering skills used to protect modern enterprise environments.
Firewall Configuration and Hardening
Hands-on configuration and management of firewalls including policy creation, access control, and threat prevention techniques.
SIEM Deployment and Integration
Understanding how to deploy SIEM solutions, integrate log sources, and enable centralized monitoring and detection.
Identity and Access Management (IAM)
Learning how to manage user identities, roles, and access controls to ensure secure authentication and authorization.
DLP and Email Security Implementation
Implementation of data loss prevention solutions and email security controls to protect sensitive data and prevent phishing attacks.
- Our Approach
Implementation-Focused Learning for Real Security Environments
This learning approach is designed to give you real-world experience in configuring, deploying, and managing security systems using industry tools and enterprise-level scenarios.
Hands-On Practical Training
Students work directly on real security tools and configurations to gain practical experience.
Implementation-Focused Learning
Focus on building and configuring systems rather than theoretical concepts.
Real-World Use Cases
Exposure to real enterprise scenarios and deployment environments.
Tool-Based Experience
Working with industry-standard security solutions used in organizations.
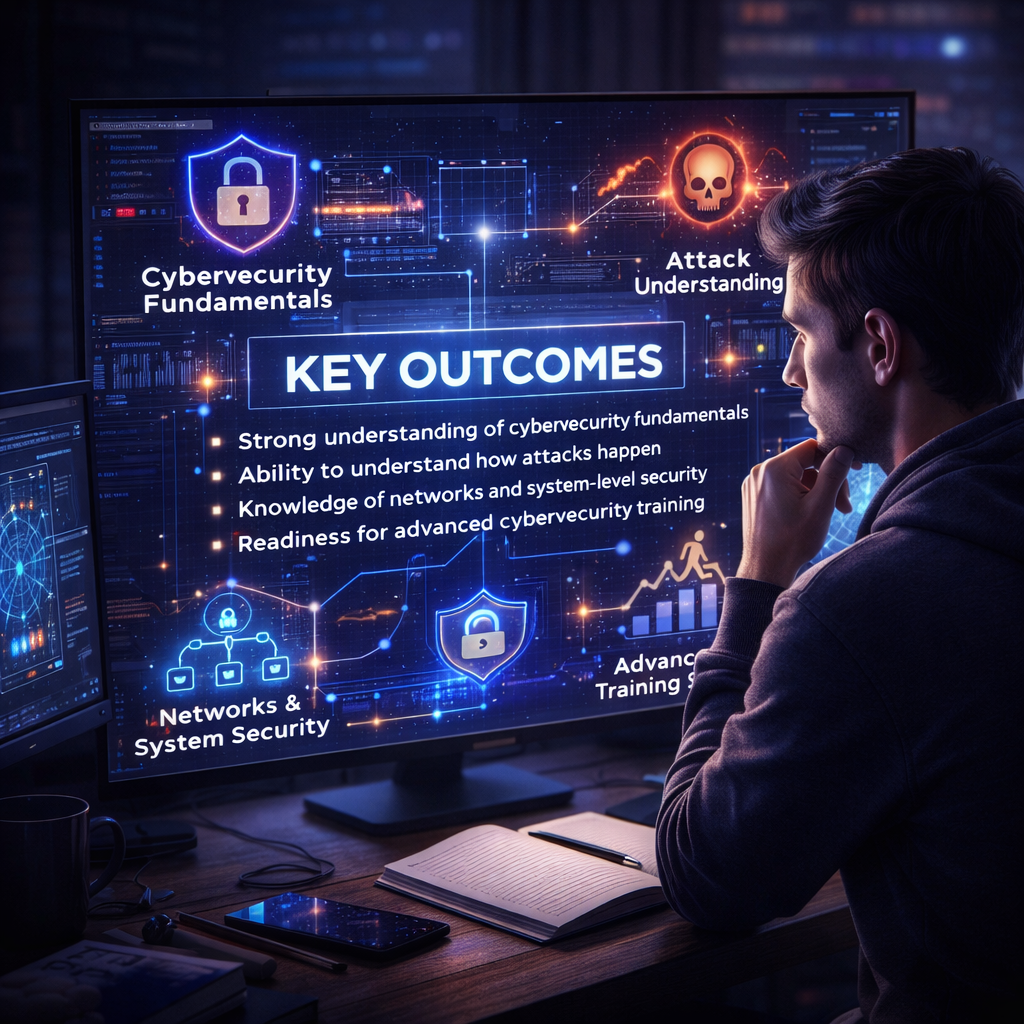
Key Outcomes
Ability to configure and manage security infrastructure
Practical experience in firewall, SIEM, and IAM implementation
Understanding of enterprise security architecture
Readiness for roles in security engineering and implementation
Why This Module Matters
Organizations require professionals who can not only identify risks but also implement solutions. This module bridges the gap between theory and real-world deployment skills.
