- welcome to RootSecured
Next-Generation Cybersecurity
for a Threat-Driven World
RootSecured delivers advanced cybersecurity solutions powered by real-world attack simulation, intelligent threat detection, and enterprise-grade security engineering — ensuring your business stays protected, resilient, and future-ready.
Proven protection
Active client with positive reviews
Our Partners



















- our Value
Security That Thinks Like an Attacker
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis.
01
Offensive Security
Simulate real-world attacks to uncover hidden vulnerabilities before attackers do.
02
Threat Intelligence
Gain actionable insights on emerging threats, attackers, and exposed assets.
03
24x7 SOC Monitoring
Continuous monitoring, detection, and rapid incident response.
04
Security Engineering
Design and implement scalable, enterprise-grade security infrastructure.
- About us
Cybersecurity Built for Modern Enterprises
At RootSecured, we go beyond traditional security approaches. Our team of cybersecurity experts combines offensive security, real-time monitoring, and advanced engineering to protect organizations from evolving cyber threats.
We don’t just identify risks — we simulate real attacks, build resilient systems, and ensure your business is always one step ahead.
24/7 monitoring

- our Core Services
Comprehensive Cybersecurity Solutions
End-to-end protection across your infrastructure, applications, and users.
01
Offensive Security
Simulate advanced cyberattacks to identify exploitable vulnerabilities and strengthen your defenses.
Cyber Threat Intelligence
Stay ahead with real-time insights into threat actors, dark web activity, and digital risks.
02
Cloud Security
Secure your cloud environments with advanced architecture, monitoring, and misconfiguration protection.
03
Security Engineering & Implementation
Design, deploy, and optimize enterprise-grade security solutions across your infrastructure.
04
Application & DevSecOps Security
Integrate security into your development lifecycle and protect applications from modern threats.
05
- OUR PRICING PLAN
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Basic Package
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec
$ 900
- 24/7 Support Service
- Encrypted transactions
- Free hardware included
- Automated daily backup
- Engagement session included
Premium Package
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec
$ 1200
- 24/7 Support Service
- Encrypted transactions
- Free hardware included
- Automated daily backup
- Engagement session included
Deluxe Package
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec
$ 1800
- 24/7 Support Service
- Encrypted transactions
- Free hardware included
- Automated daily backup
- Engagement session included
- OUR PEOJECTS
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
- Creative
Security Enhancement for Smart Devices
- Programming
Enabling Medical Staff To Prescribe
- Cyber
Enabling Medical Staff To Prescribe
- our Solution
Tailored Cybersecurity Solutions for Every Business Need
From application security to enterprise risk management — our solutions are designed to protect every layer of your digital ecosystem.
Application Security
Secure your applications, APIs, and mobile platforms against modern cyber threats.
- Web Application Security
- API & Web Services Security
- Thick Client Security
- Mobile Application Security
- ERP / SAP Security Testing
IT / IoT / OT Security
Protect infrastructure, devices, and industrial environments from advanced attacks.
- Network & Security Devices
- VoIP Security
- Wireless Security
- IoT / OT / SCADA / ICS Security
- Endpoint Security
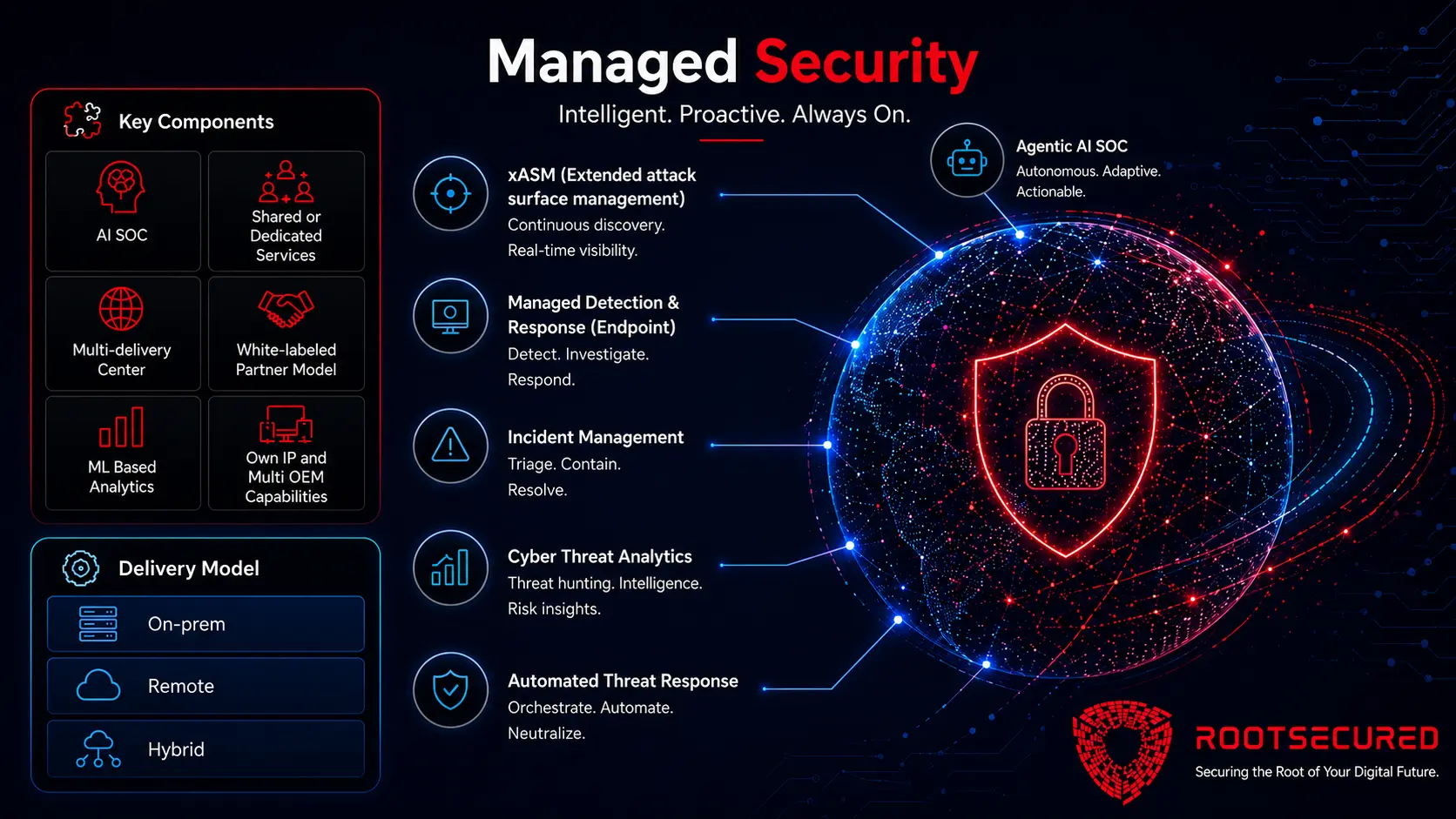
Cloud & Managed Security
Secure your cloud infrastructure and digital assets with continuous monitoring and protection.
- Digital Forensics
- Phishing Protection
- Container Security
- Kubernetes Security
- Vendor / Supply Chain Security
- Security Posture Management
- GRC Automation
Cyber Risk Management
Identify, assess, and manage cyber risks aligned with your business objectives.
- Red Teaming
- Virtual CISO (vCISO)
- Data Protection Officer (DPO)
- SMB Security Solutions
For Startups
Affordable, scalable cybersecurity solutions designed for fast-growing startups.
- Startup Security Packages
- Compliance Readiness
- Cloud Security Setup
- Continuous Monitoring
Need a Customized Security Solution?



- SOC
24x7 Security Operations Center (SOC)
Our SOC-as-a-Service provides round-the-clock monitoring, advanced threat detection, and expert-led incident response — ensuring complete visibility and protection across your environment.
24x7x365 Monitoring
Real-time Threat Detection
SIEM + Threat Intelligence Integration
SLA-driven Incident Response
Our Clients

















- our testimonials
- book now
Don’t Wait for a Breach to Act
Cyber threats are evolving every day. Stay ahead with proactive security strategies and expert-driven protection.
- Book Now
Don’t Wait for a Breach to Act
Cyber threats are evolving every day. Stay ahead with proactive security strategies and expert-driven protection.
- How We Work?
Precision in Process, Perfection in Protection
At RootSecured, our approach to cybersecurity is both strategic and simple. We focus on making security seamless, transparent, and above all, effective. Here’s how we protect your business, step by step:
We start by understanding your organization thoroughly – from infrastructure to workflows. Our detailed discovery process uncovers vulnerabilities and areas of risk, helping us understand your security needs at every level.
Based on what we uncover, we create a security plan specifically suited to your business. This isn’t a generic approach – we design a solution to address your exact challenges, whether it’s IT, OT, or IoT, ensuring all your assets are secure.
Instead of waiting for threats to emerge, we put in place advanced, proactive defense systems. Our tools continuously monitor your environment, using cutting-edge technology to detect and neutralize potential risks before they impact your business.
Once the security strategy is set, we integrate it smoothly into your existing systems with minimal disruption. Our seamless implementation ensures that your cybersecurity measures are up and running without affecting your day-to-day operations.
Cybersecurity doesn’t stop after implementation. With our 24/7 SOC (Security Operations Center) and NOC (Network Operations Center), we continuously monitor your systems. If an issue arises, we respond instantly to neutralize threats and keep your business safe.
Cyber threats are constantly evolving, and so is our approach. We continuously reassess and adjust our security measures to stay ahead of emerging threats. This adaptability keeps your business secure and resilient, no matter how the threat landscape shifts.
We prioritize clear, actionable insights. You’ll always have access to detailed reports showing how our solutions are making a measurable difference in reducing risk and improving your overall security posture.
Cybersecurity is an ongoing journey. We’re committed to being a long-term partner, not just a one-off service. As your business grows and faces new challenges, we’ll be right there, helping you stay secure, resilient, and prepared.
- our team
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
- FAQ
Get Answers to
Phishing is the most common cyber-attack. Some of the other typical ones include Malware, Ransomware, Denial-of-Service (DoS) attacks, Man-in-the-Middle (MitM) attacks, SQL injection, Cross-site scripting (XSS), and Zero-day exploits.
They can include hackers, hacktivists, nation-states, cybercriminals, cyber terrorists, and script kiddies.
The different services we provide are Risk and Compliance services, Virtual CISO services, Threat detection, proactive threat monitoring services & advanced threat protection, cybersecurity consulting services, managed security services, Risk management, and Risk assessment services, managed detection and response, etc.
We offer a comprehensive range services including, Managed Security Services, Technology Consulting & Transformation Services, and Cyber security Assessment Services. Our MSS umbrella covers Security Operations Center (SOC) services, Managed Detection and Response (MDR), Vulnerability Management, IT Infrastructure Support, Helpdesk, and Compliance Services. Our solutions are designed to protect your organization from evolving cyber threats.
The key areas of data security are Network Security, Application Security, Endpoint Security, and Identity and Access Management (IAM).
- Blog
From Vulnerabilities to Impact: The…
Vulnerability Assessment and Penetration Testing (VAPT) is more than just running automated…
Beyond Alerts: The Human Intelligence…
A Security Operations Center (SOC) is often perceived as a hub of…
Thinking Like an Attacker: The…
Secure code review is not just about verifying functionality — it is…


